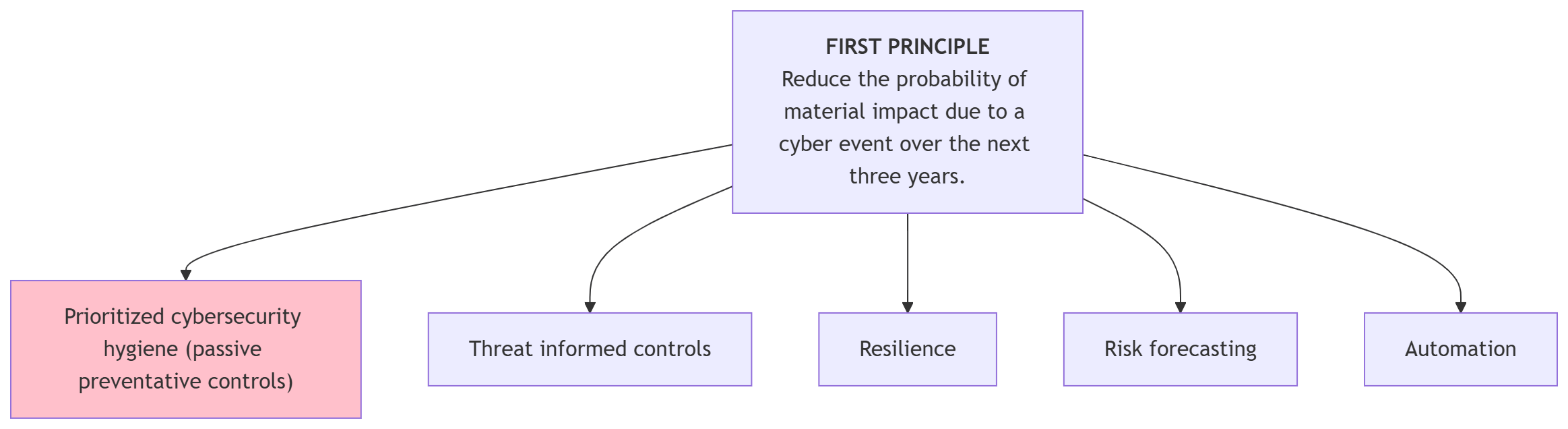
In my last post, we talked about why your security program needs a map before a toolbox. To move towards our goal of reducing the chance of a cybersecurity event that can hurt our organization, we need to start with prioritized cybersecurity hygiene.
What is prioritized cybersecurity hygiene?
Think of cybersecurity hygiene like building a house. You don’t wait for a storm to decide if you need a roof. You put the roof on because that’s just how you build a sturdy house. You probably put locks on your doors and windows too, regardless of the crime rate.
In IT, prioritized hygiene is a set of configuration decisions. These are best practices that you should follow no matter what. It doesn't matter if you think a hacker is targeting you today or not. These controls stay "on" in the background, quietly protecting your environment by deterring and thwarting threats.
CIS Controls: community-driven alignment on cyber hygiene
To know where to start, we look at the CIS Controls Implementation Group 1 (IG1).
The Center for Internet Security (CIS) calls these "essential cyber hygiene." They aren't just "good ideas":
CIS defines a Control as a broad security objective, representing a major area of focus for securing an organization.
A Safeguard is a specific, actionable task or requirement nested within a Control.
The Safeguards in IG1 are what every organization should implement to defend against the most common attacks.
Scoped with small/medium organizations in mind, who typically have limited IT and cybersecurity expertise.
I personally love the CIS Controls and related Safeguards because they are clearly written and actionable.
By following IG1, you focus on the basics that stop the most common, non-targeted threats.

The Boondock Saints’ take on cybersecurity hygiene.
Examples of passive preventative controls
Passive preventative controls are the settings and rules you set and review periodically when guidance changes. Some examples are:
Inventory of Assets: You can't protect what you don't know you have. Keep a list of every device, identity, cloud resource, and software application in your organization.
Phish-resistant MFA: Provides strong authentication and prevents account takeovers.
Disk encryption: If a laptop is stolen, the data stays locked. This is a configuration choice that protects you 24/7.
Secure Configurations: Don't use the default settings that come out of the box. Change passwords, urn off features you don't use, and review publicly available guidance on recommended configuration.
Continuous Vulnerability Management: Set your systems to scan for weaknesses and patch them automatically. Automatic software updates are your friend, particularly on client devices.
We’ll get into the details of these types of controls in future posts, but these controls are tactics we are choosing to support the strategy.
Why passive preventative controls come first
In personal health, hygiene is washing your hands, brushing your teeth, bathing, and staying away from others who are contagiously ill. All of these things reduce the chances of you getting sick.
Much like a germ and your body, in the cyber world hygiene is about making your environment inherently difficult to invade. You are establishing a holistically hardened environment. You are closing most of the paths that cause most cybersecurity events.
In my next post, we’ll move past the basics. We’ll talk about how to use Threat-informed controls to disrupt specific attack patterns.
Resources
CIS Critical Security Controls | cisecurity.org
CIS Critical Security Controls Implementation Group 1 | cisecurity.org
