Table of Contents
Phone calls are the new phishing (aka “vishing”)

New data shows that hackers are moving away from bulk emails. Instead, they are using phone calls to trick employees and IT teams into giving up network access.
Why it matters: IT help desks are a major target for these calls. Hackers often pretend to be an employee who lost their password or needs help with a login. If the help desk skips a security step, the hacker can get full control of a business account.
The big picture: A new report from Mandiant shows that phone-based attacks made up 11% of all security incidents last year. While hackers still use software bugs to get into networks 32% of the time, phone scams are becoming more common. Email phishing has dropped to only 6% of attacks because companies have become better at blocking bad emails.
Steps you can take now to reduce your risk:
Verify every caller. Create a rule that help desk staff must verify a caller's identity before resetting a password. You can use a manager approval or a pre-set secret code. My favorite is callback verification at a the phone number you have on record for the caller.
Train your team on pressure tactics. Scammers often act like they are in a rush or angry to make you skip safety rules. Remind your team to slow down and follow the process.
Use strong security keys. Switch to phishing-resistant security keys or passkeys. These can’t be stolen over the phone. However, any calls to re-enroll a security key should use the same caller verification process as a password.
Monitor for new logins. Watch for any login that happens immediately after a password reset, especially if it comes from a new location. Depending on your identity and logging platforms, you may be able to configure an alert for this.
Go deeper: Read the full report on the CyberScoop website to learn more about how these tactics are shifting.
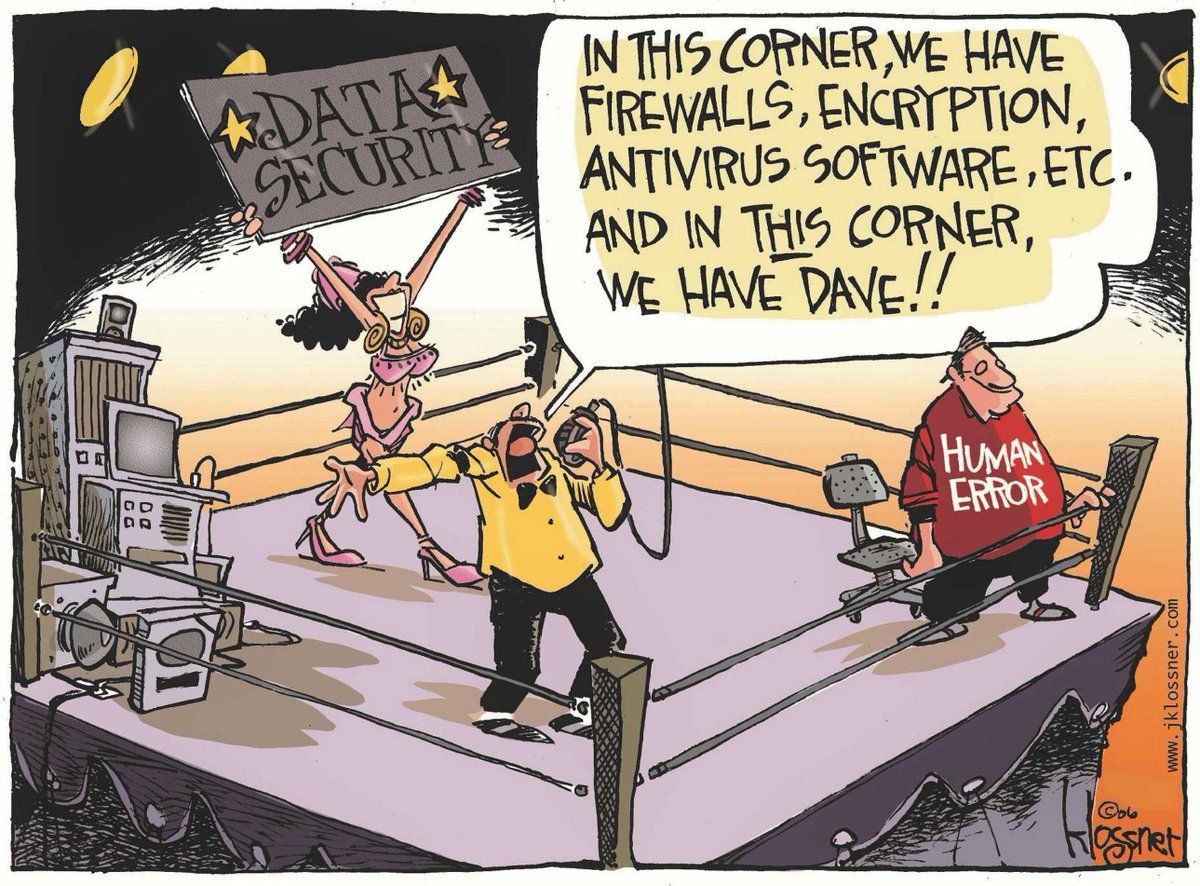
Human instincts create security risks
New research shows that our brains are not wired for the digital world. When people feel rushed or scared, they often make quick mistakes instead of following safety rules.
Why it matters: Security software cannot always stop a person from instinctually picking familiar, immediate choices rather than the ones that serve them or your organization best. Adversaries know this and design their social engineering tactics with this in mind.
Big picture: Our brains use "cognitive narrowing" during stressful moments. This means we focus on immediate fixes and ignore warning signs like strange email addresses. Attackers send fake password reset notes to cause panic, making users more likely to walk into a trap.
Steps you can take now to reduce your risk:
Provide a password manager. This tool helps your team use unique passwords without needing to remember them. If you can’t afford something like Bitwarden, even using the password manager built in Edge or Chrome with a managed work identity is better than nothing.
Stop forcing password changes. Frequent changes often cause people to pick simple, weak passwords. This is in NIST’s official guidance (SP 800-63B, 3.1.1.2., item 6).
Use multifactor authentication (MFA). Set up the strongest form of MFA available for every application and remote connection your team uses.
Switch to passkeys. Passkeys are phish-resistant, removing the risk of stolen passwords by changing how users log in and phishable forms of MFA challenges.
Run monthly training. Short, monthly lessons help employees stay alert and change their habits over time.
Go deeper: Read the full report on the Marisec Intelligence website to learn more about the psychology of cyber threats.
CIS releases Iran cyber defense playbook

Recent military activity in the Middle East has led to more cyberattacks from Iran. These attacks are not usually meant to cause one big disaster. Instead, Iran uses a steady stream of smaller attacks to create long-term problems for US organizations.
Why it matters: Iranian hackers often target local government groups and critical businesses. They use simple methods to get into a network, such as stealing passwords or tricking people with emails. Once they gain access, they can steal data or use "wiper" software to delete your files and stop your work.
The big picture: Hackers from Iran look for easy ways into your network. They search for devices that you have not updated or accounts that do not have extra security. They also use "Living off the Land" tactics. This means they use your computer's own built-in tools to hide their tracks and stay in your network for a long time.
Steps to take now to reduce your risk:
Update your devices immediately. Focus on tools that connect to the public internet. You should prioritize your VPNs, firewalls, and email servers.
Require multifactor authentication (MFA). Noticing a recurring theme? Turn on MFA for every account in your company. You should also audit your service accounts to make sure they are secure.
Watch your logs. Look for signs of "password spraying." This is when a hacker tries one common password on many different accounts.
Prepare your leaders. Scammers often target executives with personalized emails to steal their login details. You should train your staff to spot these fake messages.
Protect your backups. Keep copies of your data in a safe, offline location. This helps you recover if a hacker deletes your live files.
Go deeper: You can find the full list of technical steps and tracking updates on the CIS website.
Hackers target edge devices more often than before

VulnCheck released its 2026 report on the security of "edge" devices like routers, firewalls, and VPNs. The data shows that attackers are finding ways into these tools faster than IT teams can fix them.
Why it matters: Edge devices are the doors to your business network. If they are not secure, hackers can enter and steal your data. Many IT teams only watch the government's "Known Exploited Vulnerabilities" (KEV) list to decide what to patch. However, that list misses over 75% of the bugs hackers actually use to attack edge devices.
The big picture: Adversaries focus on "end-of-life" devices. These are old products that no longer get security updates from the maker. In 2025, about 42% of attacks hit these old tools. Botnets also target this gear to build their networks.
Steps to take now to reduce your risk:
Replace old hardware. If your router or firewall is past its "end-of-life" date, it does not get security patches. This leaves your network open to hackers.
Look beyond the government list. Use other threat data sources to find out which bugs hackers are using. The CISA list is a good start, but it does not show the whole picture.
Separate your network. Use network segmentation to keep your edge devices away from your most important files. If a hacker takes over a router, they will not have an easy path to your data.
Limit what devices can do. Give each tool only the access it needs to do its job.
Go deeper: Read the full "Exploring the Network Edge" report on the VulnCheck website.
New FCC rules ban new foreign-made routers

On March 23, 2026, the FCC added new foreign-made routers to its list of equipment that poses a national security risk. This means new models of these routers cannot get an FCC ID. Without that ID, companies cannot sell or import them in the United States.
Why it matters: Federal agencies worry that routers made in other countries could have hidden security holes. Adversaries could use these holes to hurt power grids, water systems, or national defense. By stopping new models from entering the country, the government hopes to protect these important systems from cyberattacks.
The big picture: The rules apply to any router where a major step (like design, development, or assembly) happens outside the United States. It does not matter if a U.S. company designed the device; if it was made abroad, it is likely covered by this ban. However, the ban only affects new models. Any router model that already has an FCC ID is still legal to buy, sell, and use.
Steps to take now:
Verify your current routers. Look for the FCC ID on your office devices. If they have one, you can keep using them without worry.
Check before you buy. If you are planning to upgrade your network, ask the seller if the new model is made in the U.S. Only new models made in the United States or those with a special "Conditional Approval" from the government are allowed.
Install software updates. The FCC still allows firmware and software updates for these routers. You should keep your current gear updated to fix known security bugs.
Look for exemptions. The Department of Homeland Security (DHS) can grant approvals for certain foreign routers if they show the devices are safe.
Go deeper: You can read the full list of rules and definitions on the FCC website.
Thanks for reading and stay secure,
Aaron