Security automation is the fifth and final part of a strong cybersecurity strategy. It is the process of using computers and software systems to handle security tasks without a person doing every step by hand. For a small IT team, automation is not just a helpful tool. It is a requirement to keep up with modern threats.
Why automation is a requirement
Most IT teams have already changed how they work. They use tools to set up servers, workstations, and networks quickly. However, security often stays slow because it still relies on manual work. When security tasks are manual, they become "toil".
Toil is work that is repetitive and does not have long-term value. It also leads to human error. Hackers use these small mistakes to get into your network. Automation removes this toil. It lets your team focus on more important security goals instead of doing the same tasks every day.
Infrastructure as Code
In the past, setting up a server required a person to click through many screens. Today, IT pros use "Infrastructure as Code" (IaC). This means they write software files that tell the computer how to set up the system. Because these systems are built with code, they are easy to repeat and hard to break.
Automating compliance
Compliance means following the laws and rules for your industry, such as HIPAA or CCPA. These rules are a "ticket to ride" for doing business, but they do not always make you safer. Proving that you follow these rules usually takes a lot of manual work and paperwork.
You can use "Policy as Code" to automate this work. Write scripts that check your systems every day to see if they still follow the rules. If a setting changes and breaks a rule, the system can fix itself or alert you immediately. This saves your team hundreds of hours and ensures you are always ready for an audit.
Practical examples of security automation
There are many ways to start using automation in your daily work:
Software updates. Configure your systems to automatically check for and install security updates for operating systems and applications.
Configuration management. Use technologies that all you to define settings once and apply/enforce everywhere, such as on-premises Active Directory group policy or cloud-based Intune configuration profiles. Certain network technologies, like Cisco Meraki, can apply configuration templates to multiple networks.
Automated backups. For endpoints this may be cloud sync technology for files, or policy-based backup tools for virtual servers.
Make automation your standard
Automation is the only way a small team can stay ahead of modern hackers. When you build security into your processes with system automation, you remove the errors that happen when people are busy or tired. This shift lets you focus on goals and problems that benefit from human attention.
What’s next
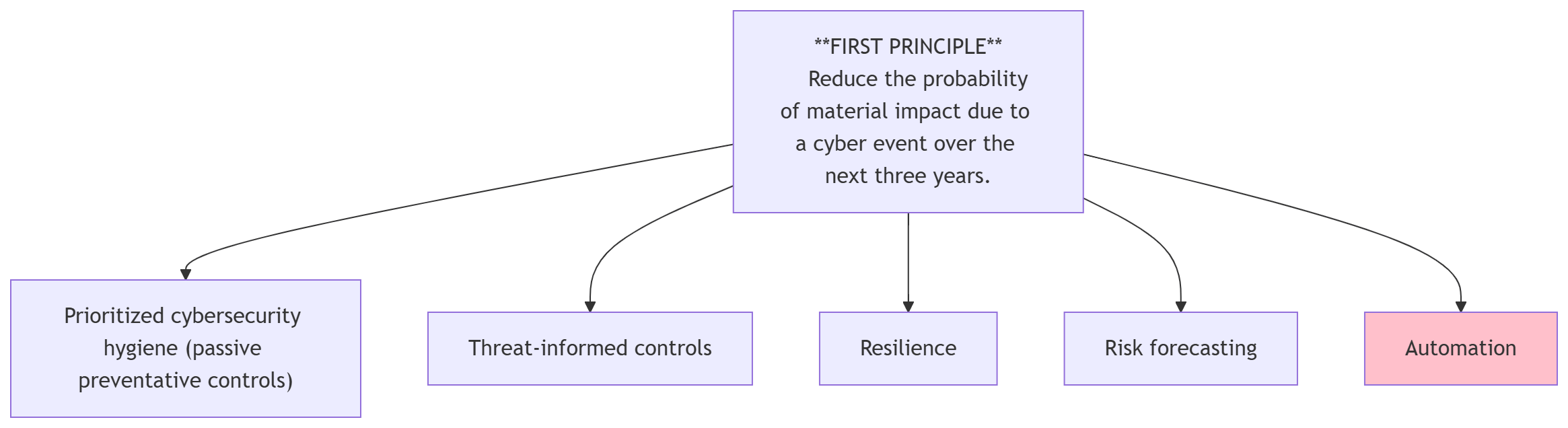
OK. We’ve gotten through the five foundational strategies that help us pursue our cybersecurity first principle, to “Reduce the probability of material impact due to a cyber event over the next three years.”
Going forward, we will dive into the tactics (the specific actions you take to support the strategy), always tying them back to one (or more) of these strategies.
Thanks for reading and stay secure,
Aaron
